Trojans Troubleshooting
Reader Question:
“Hi Wally, I am having problems with Trojans and wondering how to fix it?” - Bianca C., USA
Before addressing any computer issue, I always recommend scanning and repairing any underlying problems affecting your PC health and performance:
- Step 1 : Download PC Repair & Optimizer Tool (WinThruster for Win 10, 8, 7, Vista, XP and 2000 – Microsoft Gold Certified).
- Step 2 : Click “Start Scan” to find Windows registry issues that could be causing PC problems.
- Step 3 : Click “Repair All” to fix all issues.
Setting up weekly (or daily) automatic scans will help prevent system problems and keep your PC running fast and trouble-free.
Wally’s Answer:
Overview of Trojans
One of the most prevalent malicious software programs is known as a “Trojan.” Trojan is short for Trojan Horse. The name comes from the Greek myth because it uses similar methods to gain access to a computer. The Trojan program often appears to be a trusted or harmless program.
Trojans are frequently attached to emails and the user triggers their installation when they attempt to open or download the attachment. Trojans often appear to be pictures or important documents.
Once the Trojan has downloaded to the computer it may immediately install or it may wait a predetermined amount of time before it installs. Sometimes Trojans are programmed not to install until another program on the computer is started.
Hackers often use Trojans to take control of computers and use them to perform automated spamming or participate in denial of service attacks on websites. They can also be used to steal data from the computer or install other malware.
Trojans can also be delivered to computers through Internet browsers. Sometimes they exploit a known vulnerability in the browser or a website. Other times, they pretend to be an advertisement or video.
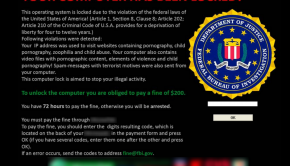
What Problems are Associated with Trojans?
One of the most common Trojan related messages a user will encounter is, “Your computer was infected by unknown Trojan.” This often appears after a website conducts a free scan of the computer. It may also appear if the user has downloaded and installed a fake spy-ware program. Often this message is really a scare tactic to induce the user to purchase specific Trojan removal software.
Before purchasing any Trojan removal software, a user should research the products they are considering. Be certain that the product has a reputation for being able to do what it claims and industry experts are attesting to the legitimacy of the product. Many of the fake Trojan removal software has a lot of testimonial reviews of their product all over the Internet, but they do not have legitimate computer technology sites, like CNet or PCMag, review their fake offering.
Some of the Trojan programs that are often used by hackers include Netbus, Y3K Remote Administration Tool, Beast, Zues, and Flashback Trojan. Most of these popular Trojan programs can be easily removed with reputable Trojan removal software. Some will require the user to manually delete some files from the infected computer.
I Hope You Liked This Blog Article! If You Need Additional Support on This Issue Then Please Don’t Hesitate To Contact Me On Facebook.
Is Your PC Healthy?
I always recommend to my readers to regularly use a trusted registry cleaner and optimizer such as WinThruster or CCleaner. Many problems that you encounter can be attributed to a corrupt and bloated registry.
Happy Computing! ![]()

Wally's Answer Rating
Summary: Every Windows Wally blog post is evaluated on these three criteria. The average of all three elements determines an "Overall Rating" for each blog post.